-
What Is A VPN Alternative?

Secure remote access to a company’s network is made possible via VPN solutions. They establish an encrypted link between the client, frequently implemented as computer software on an employee’s workstation, and a VPN gateway inside the company network. VPNs secure communication between the client computer and the enterprise gateway by encrypting traffic to prevent spying.…
-
What is DoH?
DoH functions similarly to DNS. However, HTTPS sessions save the requests and reduce the amount of data transferred when making inquiries.
-
What is Data Segmentation?
Data segmentation divides your data into at least two sections, while larger networks with sensitive data may require more divisions.
-
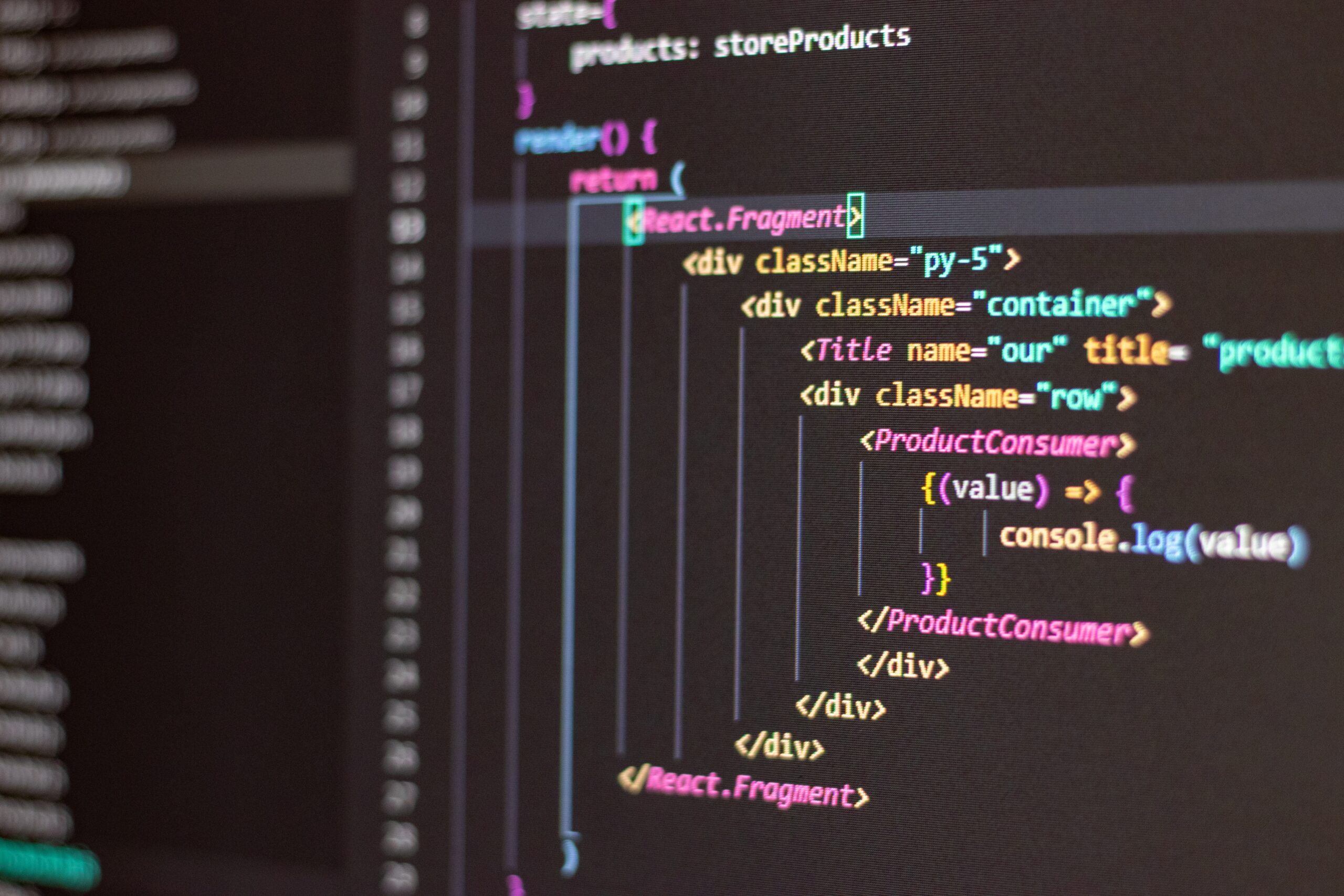
What Is Network As Code?

competitive advantage over its competitors. As the name suggests, Network as Code (NaC) is an application of the Infrastructure as Code concept to the network domain, covering traditional data centers, campus networks, wide area networks, and cloud environments.
-
What is Network Segmentation?

A network can be divided into several segments or subnets, each of which functions as a separate little network, using a technique called network segmentation.
-
What Is Secure Access Service Edge (SASE)?
With SASE, you can combine SD-WAN components such as Firewall as a Service, CASB, SWG, and ZTNA into one cloud-native device.
-
What Is Cloud Infrastructure Security?

You can find development environments in a cloud environment, managed hosting environments where various applications can be developed, and development environments for testing.
-
What is Cybersecurity?

In cyber security, hardware, software, and data connected to the internet are protected against cyber threats.
-
Hello world!
Welcome to WordPress. This is your first post. Edit or delete it, then start writing!